Hadrian is a leading provider of offensive security automation, delivering a modern, hacker-style approach to external threat surface management. As the industry’s first Autonomous Security Platform, Hadrian simulates real-world attacks to uncover and prioritize exploitable vulnerabilities — allowing security teams to take a proactive, attacker’s-eye view of their digital assets.
Headquartered in Europe and trusted by global enterprises, Hadrian continuously monitors assets from the outside-in using AI, real-time intelligence, and continuous recon. For organizations in the Middle East, Hadrian supports compliance with frameworks like NCA ECC, SAMA, and GDPR by surfacing actionable risk and reducing response times across large-scale digital environments.
Autonomous Security Platform
Summary: External threat surface management through continuous offensive testing
The Hadrian Autonomous Security Platform simulates hacker behavior to identify exploitable vulnerabilities across web applications, cloud assets, APIs, IPs, and domains. It combines asset discovery, event-driven scanning, and prioritized remediation to deliver continuous security posture improvement.
Key Capabilities:
– Continuous external asset discovery with real-time updates
– Event-driven security testing (e.g., new DNS, repo commits, etc.)
– Detection of OWASP Top 10, zero-days, misconfigurations
– Custom risk scoring and contextual remediation guidance
– SaaS-based platform with no agent or integration needed
Why it matters:
Most security tools take a defensive view — Hadrian shows what attackers see. It enables organizations to identify and close high-impact exposures before they are exploited, aligning with modern risk-based vulnerability management practices.
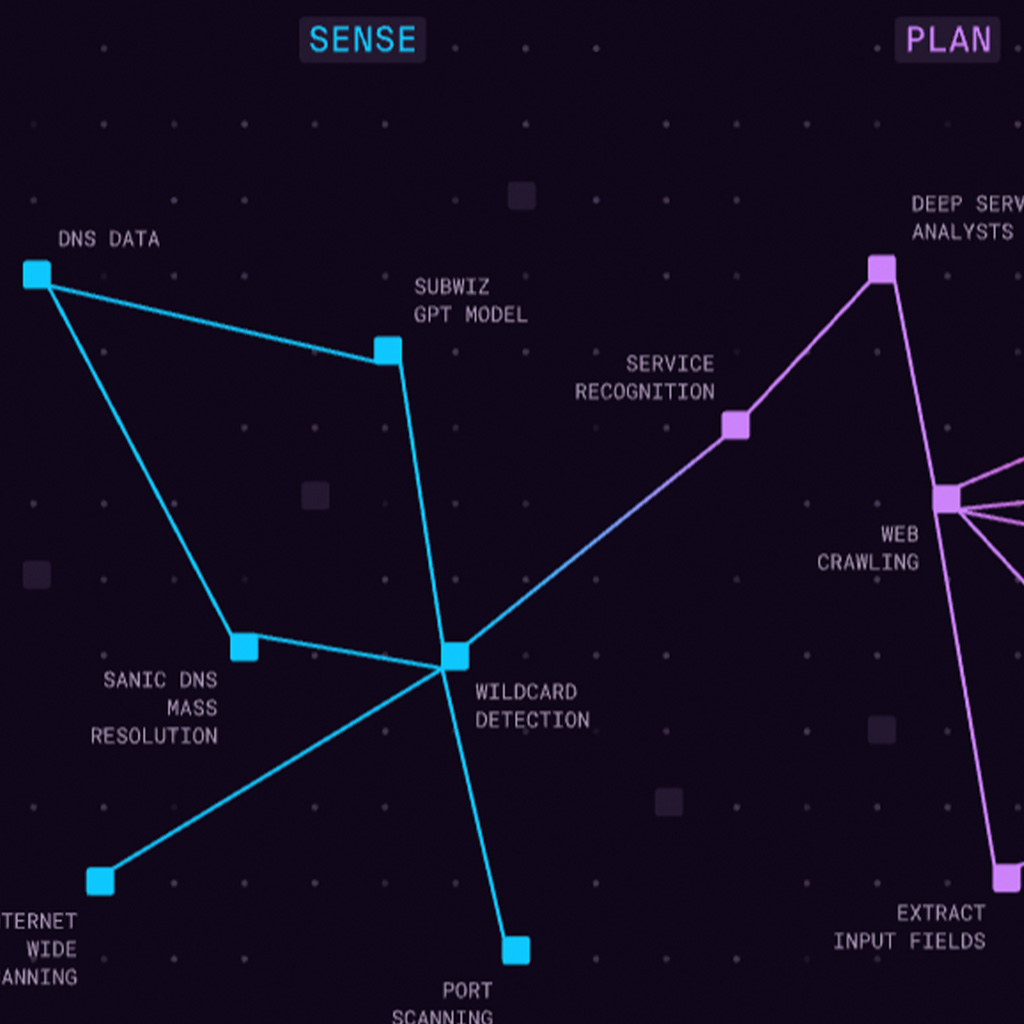
Digital Footprint Mapping
Summary: Accurate, real-time discovery of all internet-facing assets
Hadrian’s automated asset discovery engine continuously maps an organization’s digital footprint, including shadow IT, forgotten domains, cloud buckets, and exposed services — all without deploying any agents.
Key Capabilities:
– Discovery of IPs, domains, ports, web apps, SaaS services, and misconfigurations
– Continuous recon with daily updates and drift detection
– Tagging by business unit, geography, or application
– Alerting on new and unknown exposures
Why it matters:
Security teams can’t protect what they don’t know. Hadrian gives full visibility into your attack surface, including assets outside your current scope — a must-have for Zero Trust and SAMA-aligned frameworks.
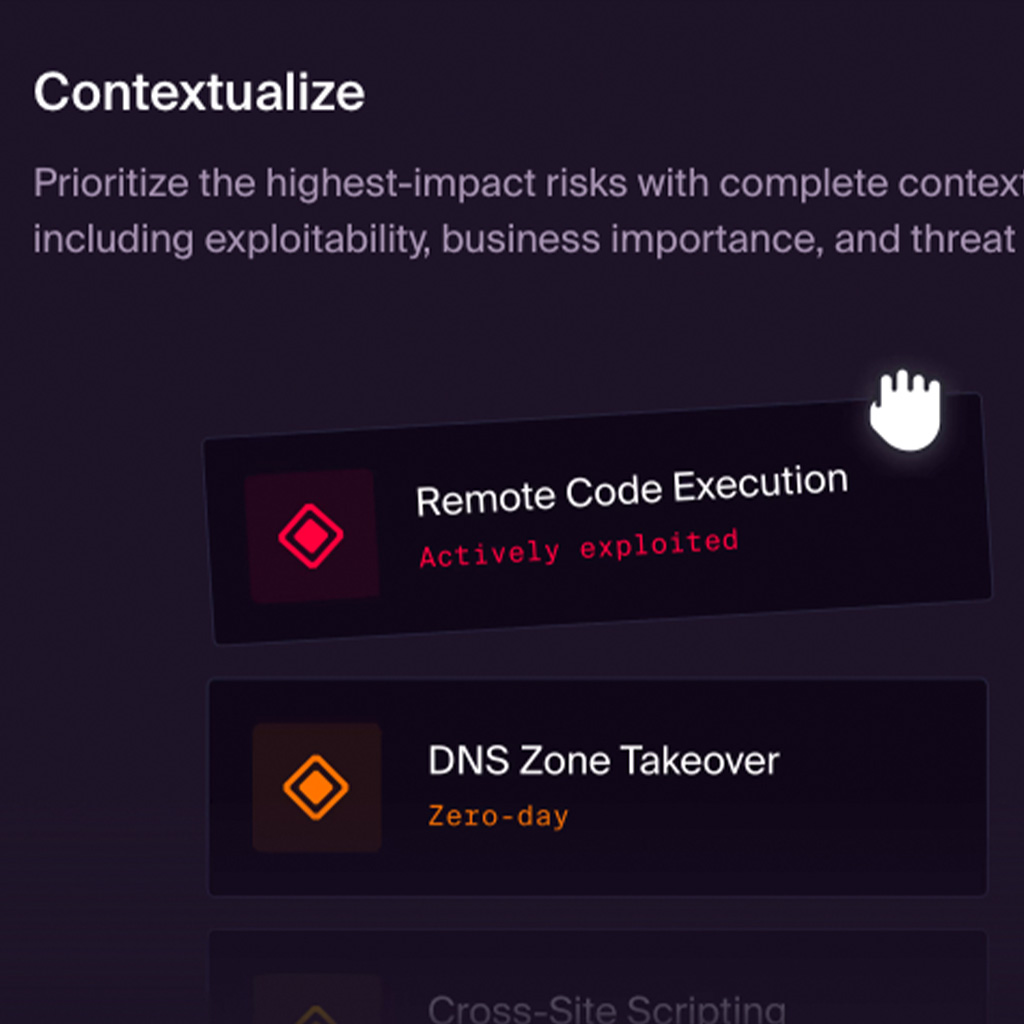
Threat Exposure Management
Summary: Real-world threat detection through simulated adversarial activity
Hadrian simulates threat actor behavior to expose true exploitable paths into your organization. Rather than overwhelming teams with CVEs, Hadrian shows which assets are actually at risk based on hacker tactics.
Key Capabilities:
– Exploitability-based testing using real-world techniques
– Detection of exposed credentials, sensitive files, admin panels
– Intelligence on infostealer-compromised systems
– Chainable vulnerability logic (e.g., open port + weak creds + outdated CMS)
Why it matters:
By surfacing only exploitable risks — not just theoretical vulnerabilities — Hadrian improves triage efficiency and ensures that remediation efforts deliver maximum risk reduction.
Event-Driven Monitoring
Summary: Real-time detection triggered by infrastructure or code changes
Hadrian’s event-driven model triggers new scans based on changes in your environment, such as new domains, updated DNS records, GitHub activity, or cloud asset changes.
Key Capabilities:
– Passive monitoring of DNS, WHOIS, GitHub, and certificate transparency logs
– Triggers attack simulations based on meaningful changes
– Reduces dwell time and improves responsiveness to change
Why it matters:
Security posture is dynamic. Hadrian’s event-driven design ensures vulnerabilities are detected as soon as they appear — not days or weeks later.
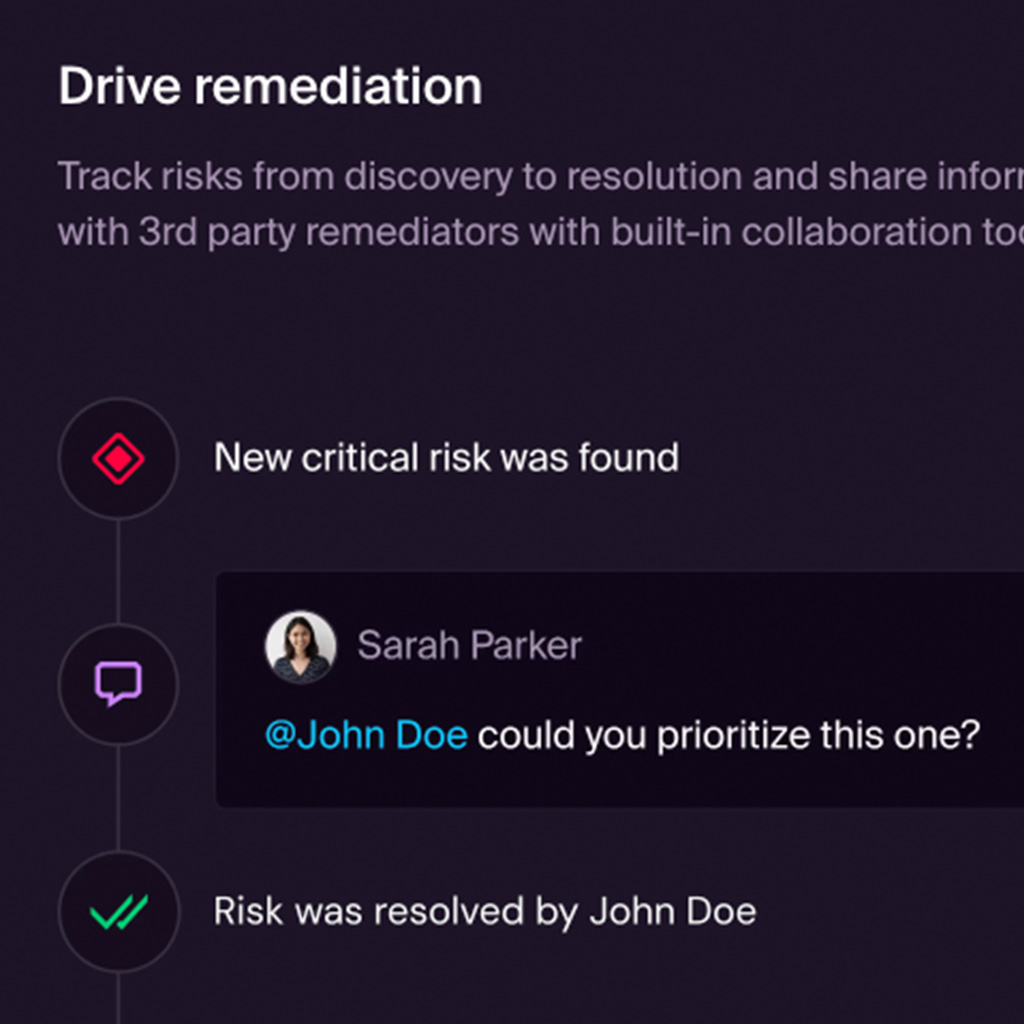
Risk-Based Remediation
Summary: Prioritized, actionable remediation tailored to business context
Hadrian delivers prioritized remediation guidance based on exploitability, asset sensitivity, and threat likelihood. The platform automatically suppresses false positives and enables teams to focus on what matters most.
Key Capabilities:
– Custom risk scoring per asset and vulnerability
– Built-in remediation playbooks and integrations (Jira, Slack, etc.)
– Suppression logic to reduce alert fatigue
– Exportable executive risk reports
Why it matters:
Hadrian helps CISOs and security teams focus on outcomes — reducing business risk and demonstrating measurable improvements over time.


